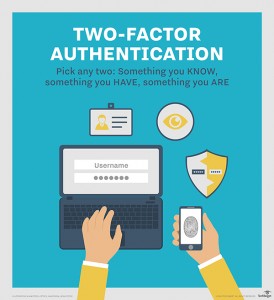
 You may have heard of two-factor authentication but what actually is it, why is it relevant to you and why do I insist you start using it today? Put simply, two-factor authentication makes it harder for people to unlawfully access your information and manipulate it. Some sample applications are as follows:
You may have heard of two-factor authentication but what actually is it, why is it relevant to you and why do I insist you start using it today? Put simply, two-factor authentication makes it harder for people to unlawfully access your information and manipulate it. Some sample applications are as follows:Banking
If you are paying someone for the first time, you’ll be asked for a code that is sent to your phone. If someone has stolen your banking logins but doesn’t have your phone, they can’t make this transfer otherwise.
Email service providers like Google Business offer the option to add verification options. They’ll ask for your cell phone number and another email account you own so that if they think you are logging in from an unusual location, for example, they’ll ask to send a text message to you to verify it really is you.
Service providers
We use an infrastructure service provider that requires that if we call them, we must give them a code to verify it’s us. This code is generated on their website, inside our login. Without this code, they won’t answer our questions or help us with matters relating to private data.
We have another service provider that sends a code to our email address when we try to log in from a place that is unusual or unexpected. In order to login, we then need to also enter the code that was emailed through.
Why bother with all of this?
The simple fact is that two-factor authentication is one of the simplest ways to protect your privacy and data, without having to do much at all.
There are so many scammers out there trying to steal your logins, data, and so on that having an easy way to make stealing your information a bit harder than others, while not great for others does protect you just a little bit better.
This is no longer just the realm of spy movies, it is the realm of amateurs and professionals alike who generate their daily income to pay their bills by stealing from you.
Common ways your data might be stolen from you
Observation
People may be watching you and observing your behaviour and sneaking a look at your phone in public places, such as on a train or bus. If you are typing your internet banking password on the train, it poses a potential opportunity for example.
 Wifi
Wifi
Data can be stolen from you over wifi networks. It doesn’t matter if your computer has a password. This is a common method to steal data.
Social engineering
This might be where someone impersonates someone else by phone or email, to steal your data. Common examples include:
- Emails purporting to be from a provider like Australia Post about an unclaimed package. This is not really from this provider but clicking on the link may download software that encrypts all your files after which a ransom is demanded to grant you access to your files again.
- Emails with links to bills, where you have to click through to pay your bill. Also zipped attachments which contain malware.
- Notices purporting to be from your bank. You get taken to what looks like your bank’s login page, but it is actually not their’ at all. Logging in doesn’t work but they have your internet banking logins by this point so their job is done.
Your information can be scraped and collated from social media such as Facebook and Twitter and very easily help to determine or deduce things about you.
Scripted phone call
With a little bit of information about you, it’s easy for a scammer to call and give the illusion they are from an organisation that you are expecting to hear from and trust. There are some key factors that help them along such as:
- How busy you are at the time – this can reduce focus and allow leakage of data more easily.
- How much you trust and believe it is that organisation calling.
- If you’re expecting to hear from them today anyway.
Combating these issues
Many institutions and enterprises are combating these things with smarter systems to help identify whether you are you, and if they don’t think that’s the case, limiting your access to do things. Some good examples of this are:
Machine learning
This takes a vast amount of data for accuracy, better in cases where the supplier has millions of customers, and ascertain automatically the most likely scenarios where accounts or information has been compromised, and utilising this to red flag future scenarios where this has likely occurred and react accordingly. For example where they identify you are logging in from a suspect location, or that you didn’t really go on a shopping spree in Las Vegas this weekend as you are also buying vegetables from your favourite local supermarket.
 Two-factor authentication
Two-factor authentication
As described in this article, a good way to help reduce the chances of private data compromise. Some other good examples of this are where you’re asked a secret question that only you know the answer to.
Location based verification
Automatically these systems can determine your likely location on the globe. If your location matches your “typical” whereabouts it’s much more likely to grant you access.
Stay safe!
Ultimately the message is, stay safe out there and be vigilant! Two-factor authentication isn’t meant to be a sexy thing, but having it means you’re going to have fewer troubles and protect the privacy and integrity of your data.

 Wifi
Wifi Two-factor authentication
Two-factor authentication